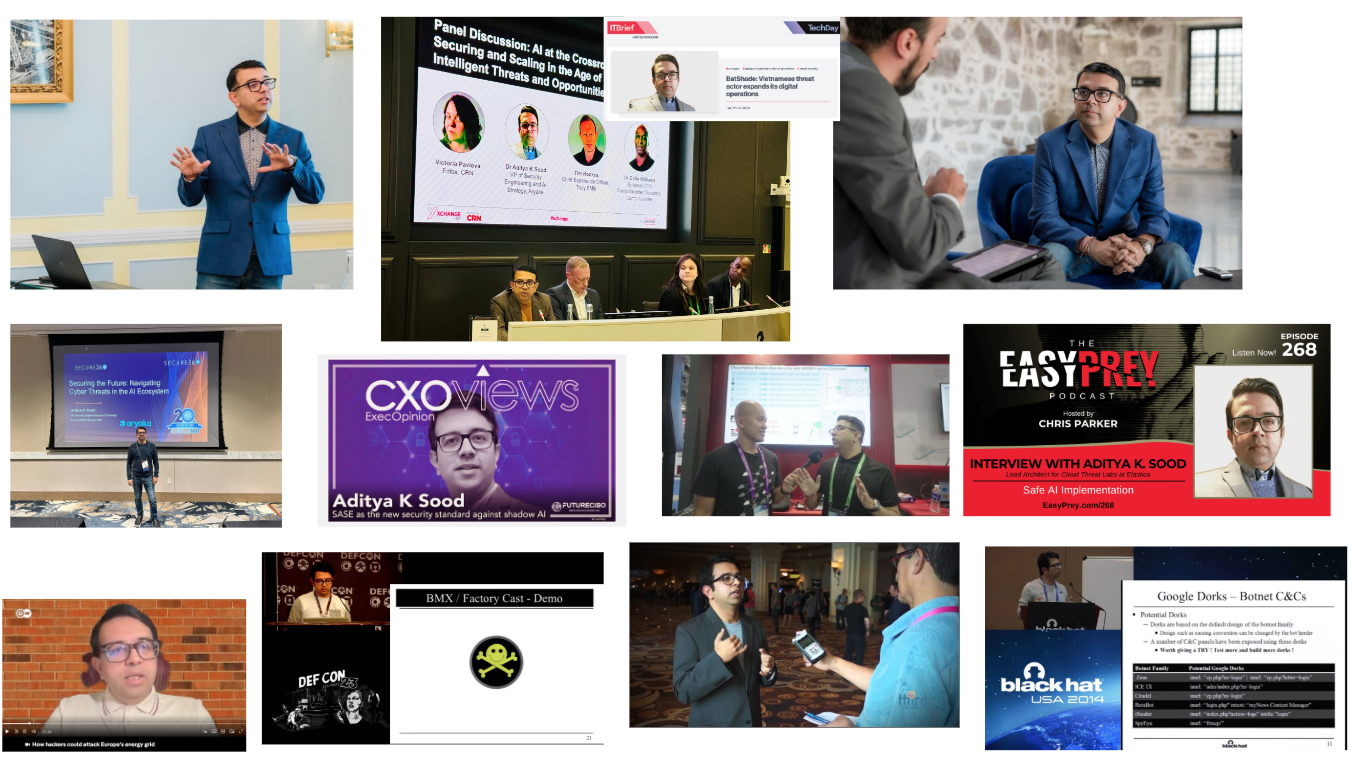
Aditya K Sood , Ph.D.
Aditya is a cybersecurity practitioner, researcher, and consultant with 18+ years of experience driving security across products and infrastructure. He specializes in aligning security with business value to enable growth and resilience. His interests include AI security, cloud security, malware automation and analysis, application security, and secure software design. He held positions such as Senior Director of Threat Research and Security Strategy, Head (Director) of Cloud Security, Chief Architect of Cloud Threat Labs, Lead Architect and Researcher, Senior Consultant, and others while working for companies such as F5 Networks, Symantec, Blue Coat, Elastica, IOActive, Coseinc, and KPMG.
At present, he is Vice President of Security Engineering and AI Strategy at Aryaka.